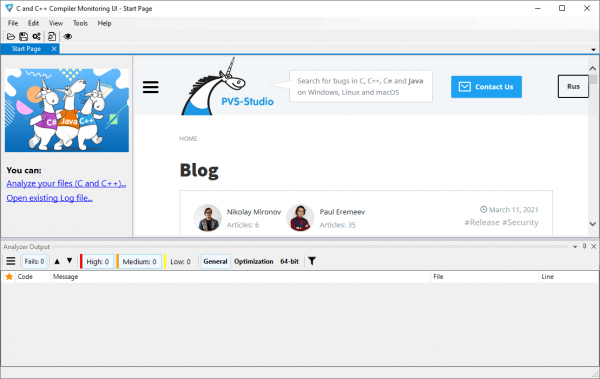
Overview of PVS-Studio 7.42.105859.2208:
 PVS-Studio 7.42.105859.2208 Crack performs static code analysis and generates reports that help programmers find and fix bugs. PVS-Studio performs a variety of code checks, and it is also useful for finding typos and copy-and-paste errors. Examples of such errors are V501, V517, V522, V523, and V3001.
PVS-Studio 7.42.105859.2208 Crack performs static code analysis and generates reports that help programmers find and fix bugs. PVS-Studio performs a variety of code checks, and it is also useful for finding typos and copy-and-paste errors. Examples of such errors are V501, V517, V522, V523, and V3001.
PVS-Studio 7.42.105859.2208 Patch is a tool for detecting bugs and security vulnerabilities in the source code of programs, which are written in C, C++, C #, and Java. The analyzer can run overnight on the server and warn of suspicious code snippets. Ideally, these errors can be detected and corrected before they reach the repository. PVS-Studio Full Version can be started automatically immediately after the compiler for newly modified files.
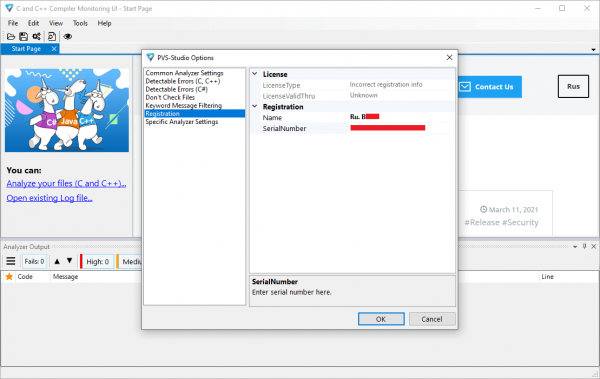
PVS-Studio 7.42.105859.2208 License Key can be integrated into the Visual Studio development environment. If you use this IDE, you will probably have to go to the PVS-Studio plugins menu and select “Check current projects”. However, this is often a more complicated process, so you will need to integrate PVS-Studio into an exotic building system. The subject of such integration is too broad to be explained here. You can find all the relevant information in our detailed documentation.
You may also like WYSIWYG Web Builder + Crack
PVS-Studio 7.42.105859.2208 Key Features:
- Simple and seamless integration with Visual Studio 2010-2019.
- Automatically scan individual files after they are recompiled.
- An online reference guide to all diagnostics available in the program, on the website, and in the documentation (presented as a .pdf file). Up to 550 pages of documentation.
- Storage and load analysis results allow overnight checks – at night, the analyzer performs the analysis and gives you the results in the morning.
- You can save scan results in HTML format with full source code navigation.
- The project analysis is executed from the command line. which helps to integrate PVS-Studio into the night development; new newspapers will be issued in the morning.
- High scalability: Support for multi-core and multi-processor systems with the ability to specify the number of cores to use; IncrediBuild support.
- Interactive filtering of analysis results (log files) in the PVS-Studio window: by diagnostic number, file name, and keyword in the diagnostic test.
- PVS-Studio 7.42.105859.2208 Keygen automatically checks for updates (while working on the IDE and building overnight).
- The BlameNotifier utility. This tool allows you to send email notifications to developers about bugs detected by PVS-Studio while running at night.
Supported languages and compilers:
- The Windows. Visual Studio 2010-2017 C, C ++, C ++ / CLI, C ++ / CX (WinRT), C #
- Windows IAR Embedded Workbench, C / C/C++ compiler for ARM C, C++
- Windows Keil µVision, DS-MDK, ARM 5/6 C compiler, C++
- Windows, Texas Instruments Code Composer Studio, ARM C, C++ code generation tools
- Windows toolchain, GNU Arm Embedded, GCC Arm Embedded compiler, C, C++
- Windows Clang C, C++
- Windows MinGW C, C++
- Windows Java
How does PVS-Studio 7.42.105859.2208 Work?
- The abstract syntax tree-based model-based analysis looks for fragments in the source code that are similar to known code models with errors.
- Method annotations provide more information about the method used than those obtained by scanning only signatures.
- Data flow analysis (data-flow analysis) is used to evaluate the limits placed on the values of variables when processing various language constructs. For example, analyzing the flow of data makes it possible to evaluate the value that a variable can take in an if / else.
- The program’s semantic model-based inference type provides the parser with complete information about all variables and instructions in the code.
- Symbolic execution evaluates the value of a variable that could be causing an error by performing a range check.
- Polluted data analysis (polluted data analysis) detects cases where the application uses unverified user data. Too much trust in this data can lead to vulnerabilities (e.g., SQLI, XSS, traverse paths).
What’s new in PVS-Studio 7.42?
(Released on 08-04-2026)
- The early access program started for new code analyzers (JavaScript and Go). The TypeScript analyzer will join the program in May. The PVS-Studio Atlas platform for managing static analysis results is also available for testing. To sign up for beta testing of the new tools, please visit the registration page.
- Support for the MISRA C++ 2023 coding standard is in progress. Twenty-two existing diagnostic rules of the MISRA group were adapted to the MISRA C++ 2023 standard. PVS-Studio IDE plugins and command-line utilities now enable selecting which MISRA C++ standard version to use. Additional information about MISRA support is available in the documentation.
- Support for free analyzer usage via special source code comments was discontinued. For more information about free licensing for open-source projects, please refer to the documentation.
- PVS-Studio plugin is now available for Qt Creator 19.x. Support for Qt Creator 13.x has been discontinued. We aim to maintain backward compatibility by supporting the latest plugin versions for all Qt Creator versions within two years of each release.
- Starting with version 4.3.0, the CMake build system includes a built-in mechanism for using PVS-Studio. For more information, please refer to the documentation.
- Further development of diagnostic rules in the Diagnosis of 64-bit errors group is discontinued. These rules may be disabled in the future. If you rely on them, please contact our support team; we will help you find an alternative solution.
- Analysis time for C and C++ template code was reduced through improvements to the template processing mechanism.
- Additional debugging mechanisms were added to the C# analyzer. If built-in .NET types cannot be loaded, a new warning (V053) will be issued. The –createBinaryLogs flag was also added to log Roslyn operations. For more information, please refer to the documentation.
- In PVS-Studio C# analyzer, an error that affected the analysis of non-SDK-style C# .NET Framework projects was fixed. This issue occurred after updating Visual Studio 2026 to version 18.4.0 or later.
- Evaluation and analysis of simple functions based on their call arguments were improved in the C and C++ analyzer.
- Preprocessing directive is present within a macro argument. This leads to undefined behavior.
- Use of externally-controlled format string. Potentially tainted data is used as a format string.
- Dereferencing the parameter without a null check. Passing the ‘null’ value to the ‘equals’ method should not cause ‘NullPointerException’.
- It is not recommended to throw exceptions from the ‘equals’ method.
Screenshots:
System Requirements:
- Operating System: Windows 7/8/10
- Processor: Pentium IV or higher.
- RAM: 2 GB RAM (4 GB recommended).
- Hard Disk Space: 2GB or more.
PVS-Studio 7.42.105859.2208 Full Version Free Download from the link given below:

